Hackers do not take a coffee break.
Therefore, understanding each cybersecurity term inside out is a must.
You might’ve heard the term ‘Secure Hashing Algorithm’ somewhere along your cybersecurity journey. So today, let’s get your curiosity cap on and understand what Secure Hashing Algorithm (SHA) is.
But before doing that, you might need to quickly run through a few terms to lay the foundation for our main star.
And to make sure, you’re at the right place for the right kind of Hash, here’s a list of topics that our comprehensive article will cover.
Let’s roll.
The internet is not a safe place anymore. Countless cyber crooks trick netizens and their e-companies into serious data breaches almost every day. Due to this, users have become cautious of their digital footprints and their overall cybersecurity measures.
Therefore, every netizen must constantly verify the authenticity of every e-attribute.
Here’s where Hashing comes in.
‘Hashing’ is a cryptographic process that is used to determine the authenticity of various inputs. Additionally, it is used to validate the integrity of your files, documents, and other types of data that floats all over the internet.
In layman’s terms, Hashing is a mathematical algorithm used to determine if the data received by you is from a genuine source. Moreover, they are used in Passwords, coding languages or SSL certificates, etc.
When used incorrectly, hashing functions could lead to lethal data breaches. However, not using them at all can lead to greater damage.
The process of Hashing uses ‘Hashes’ to verify the genuineness of the data you received. So now, Let’s understand these ‘Hashes’ closely.
A Hash is the result of a mathematical algorithm (Hash Function) that converts a simple data input into an unreadable format. This ‘Simple’ data could include any text, picture, audio, or video converted into a string of characters. And this string of characters or ‘Hash Values’ looks bizarre to the human eyes. You will see why.

Fundamentally, A hash function takes a string of inputs of any arbitrary size and converts them into unique incomprehensible data of a fixed size.
Meaning, an input data of any length will be converted into a fixed-size hash. However, if you change input values even slightly, the output hash will be completely different.
Let us first go over the ‘Unique incomprehensible data’ aspect of a Hash.
Let’s say your input data is the text ‘Security.
Below is how the Hash function of the word “Security’ will look like.
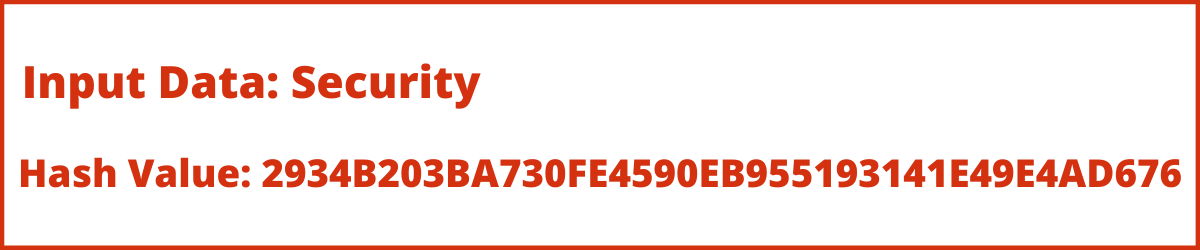
This looks nothing like the word ‘Security’ Right? Absolutely Bizarre.
Now if we change even one value of the input data the Hash output will be completely different.
Let’s say, we change ‘Security’ to ‘security’ the Hash Value will change.
Below is an example of the same.
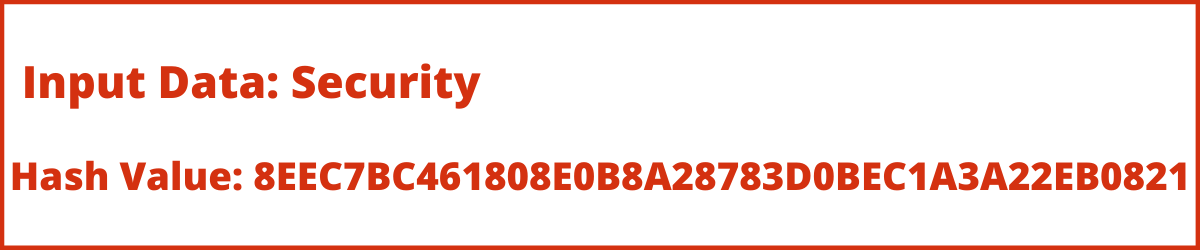
This is how a Hash generates a unique string of incomprehensible data for every slight change.
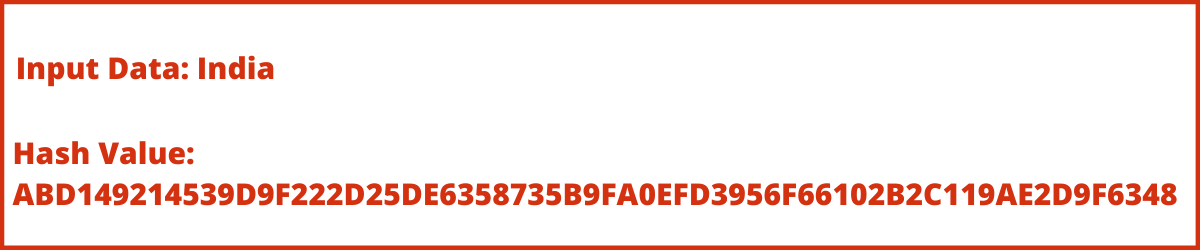
Now, let’s understand the ‘Fixed Size’ aspect of the Hash.
The above example converted the input data into SHA 1 output. These SHA 1 outputs have a 160-bit (20-byte) hash value. And, you can render them as 40 digits long. Whereas, The SHA 2 Family hash is 224 bits long. Both hash functions generate a bizarre string of a fixed size to maintain utmost security. Here’s an example.
Let’s look at the input data in

The above Hash Value string is 40 digits long. Now, let’s compare it with SHA 256 Hash which is 64 digits long.
Compare the length and uniqueness of both these strings.
The SHA1 is 40 digits long whereas the SHA2 is comparatively longer i.e., 64 Digits.
The more and unique they are, the harder it is to compromise them.
Another example of the ‘Fixed Size’ aspect would be-
No matter how long your input data is, the length of the output of both the Hashes will be as per their determined value.
The Hash Value of both inputs ‘India’ and ‘India is my country’ in SHA 1 will be 40 digits long. Similarly, for SHA 256, the value for both the inputs will be 64 digits long.
Digital Signatures need hash functions to encrypt and decrypt their data. The receiver receives these encrypted keys for further decryption.
Then the same Hash function generates a decrypted hash value. For a successful transmission, both the Hash values must be the same. This implies, that the source is authentic and reliable.
Hash functions create a unique hash value for every piece of data. Meaning, if you Hash the word ‘Elon’ it will yield a certain output. One that looks nothing like the text ‘Elon’. If you change the text ‘Elon’ to ‘ELON’ the hash value will be completely different. That’s a good hash.
If a Hash DOESN’T generate a unique output for every input, that’s a security hazard and a Broken Hash. For example, the word ‘Elon’ generates a certain Hash Value. Now, if the hash values for ‘ELON’, and ‘elon’ are the same, then do not use that Hash. It’s broken.
Alright. Since now you know what Hash and Hashing is… Let’s get to the real stars.
‘SHA’ stands for Secure Hashing Algorithm.
Here, Secure Hashing Algorithm (SHA) is the cryptographic algorithm adopted for digital signatures. It follows the ‘PKI mechanism’ to secure your data. It produces a unique hash in an unreadable format. This is to make your data secure and unhackable.
Additionally, SHA uses MD5, SHA 1, or SHA 256 for symmetric cryptography. They generate hash values to encrypt and decrypt data securely.
The MD5 or The ‘Message-Digest Algorithm’ is a one-way cryptographic function. It accepts an input of an arbitrary length and returns an output of a fixed length.
The MD5 is no longer used. This is because security experts have demonstrated techniques that state their unreliability.
SHA 1 refers to a cryptographic hash function that takes an input and produces an output of 160 bits hash value. Furthermore, they convert themselves into a 40 digits long hexadecimal number. It is also the successor to SH0.
Similarly, SHA 2 is the successor to SHA-1. The National Institute of Standards and Technology (NIST) published SHA-2 as a U.S. federal standard (FIPS).
It is originally a “family” of hashes and comes in a variety of lengths. Out of all the variety of lengths, the most popular is the SHA 256.
The various expressions of the SHA2 hashes lead to plenty of confusion. The terms “SHA-2,” “SHA-256” or “SHA-256 bit,”, “SHA-224,” “SHA-384,” or “SHA-512,” refer to the alternate bit lengths of the same SHA 2 Family.
|
SHA 1 |
SHA 2 |
|
SHA 1 was released in 1995. |
SHA 2 was released recently in 2001. |
|
It is the advanced version of SH0. |
It is the advanced version of SHA1. |
|
SHA 2 is SHA 1’s upgraded algorithm. |
SHA 3 is SHA 2’s upgraded algorithm. |
|
SHA 1 is a standalone Hash entity. |
SHA 2 has many variations. |
|
SHA 1 generates 160 bits hash value. |
SHA 2 generates 224-, 256-, 384- or 512-bits hash values. |
|
The length output value of SHA 1 is 40 digits. |
The length output value of SHA 2 is 64 digits |
|
SHA 1 is less secured when compared to SHA 2. |
SHA 2 is more secured than SHA 1 but less secure than SHA 3. |
|
SHA 1 certificates are not reliable. |
SHA 2 is more reliable because of its improved certificates. |
|
SHA 1 is not widely used. |
SHA 2 Family is widely used today. |
Your data and information on the internet can be vulnerable to cyber-attacks. Hackers can steal critical information from you about your credit card, bank account details, passwords, and more.
It’s time we netizens learn more about the security measures to safeguard our data.
We hope, our non-techie guide to SHA 1 and SHA 2 cooled down your cyber curiosity.
The End of 1-Year SSL Certificate Validity: What Organizations Need to Know