SSL certificates are widely accepted form of web server certificates to secure data in transit. As we have written much about the SSL certificates, we thought today we should let you know more about the SSL PreCertificates. We understand you may have various questions when it comes to SSL PreCertificates and as listed below, we will try to give you all your answers to it.
1. What are SSL PreCertificates ?
2. Why are SSL PreCertificates used ?
3. Limitations of SSL PreCertificates
Also read our guide on SSL Certificate for IP address.
SSL PreCertificates are a type of SSL certificates that are intended to provide proof that an SSL certificate has been logged for embedding certificate transparency (CT) data in a certificate directly. Every Certificate Authority (CA) submits this data to the Log Server as a part of Certifiate Transparency (CT). Below is how this works in-conjunction with CT.
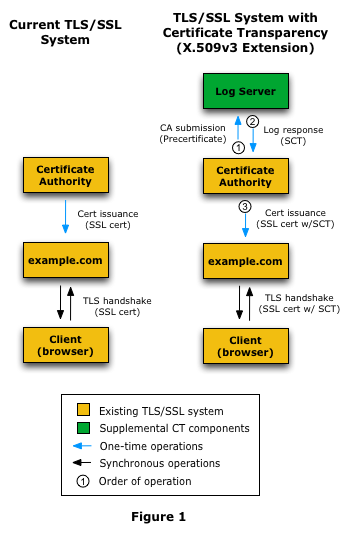
Image Credit: CT
First thing first, PreCertifiates can not be used as same as SSL Certificates to establish a secure connection. PreCertificates are never shared with the users and always are shared between the CA and the CT log authorities and in case if you have received the PreCertificates, kindly avoid deploying the same on the servers/devices.
The reason behind the issuance of SSL PreCertificates is for CT. It is a method of auditing certificate and maintaining the audit logs of certificate visible to everyone over the internet. Certificate Transparency provides proof if the certificate was issued to the domain by CA. It also makes hard for CAs to issue the certificate without the knowledge of the domain owner the Certificate Transparency aims to remedy certificate-based threats by making the issuance and existence of SSL certificates open to scrutiny by domain owners, Certificate Authorities (CAs), and domain users.
PreCertificates are issued by CAs with a unique extension OID: 1.3.6.1.4.1.11129.2.4.3, and submitted to CT Log and afterward, the CA receives an SCT (Signed Certificate Timestamp) file. This is a file signed by the log which is proof that the certificate was logged.
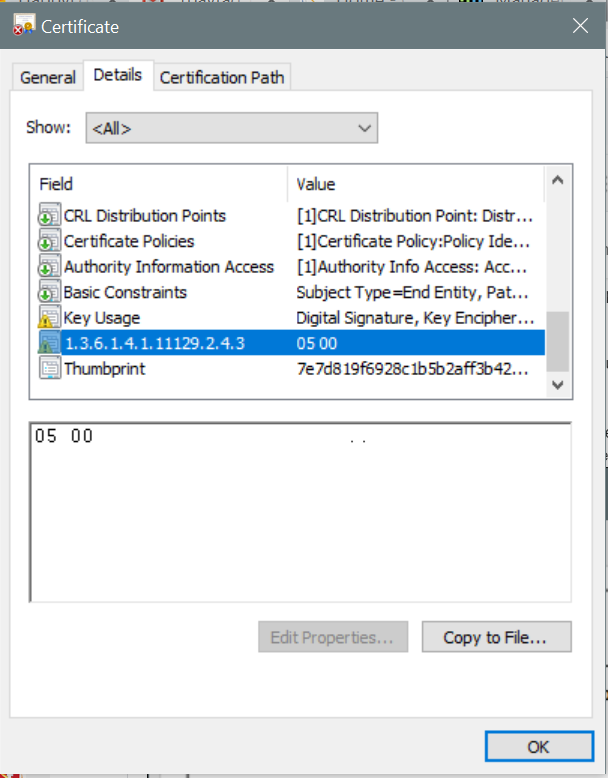
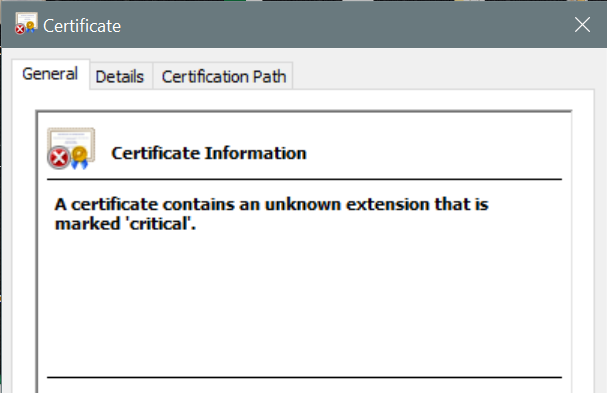
PreCertificates contain a poison extension and if deployed on the server browser will show a warning; “A certificate contains an unknown extension that is marked critical”. It means the certificate contains an extension which not recognizable by the browser and cannot be used for HTTPS connection or server authentication.
1) PreCertificates make it impossible (or at least very difficult) for a CA to issue an SSL certificate for a domain without the certificate being visible to the owner of that domain.
2) PreCertificates doesn’t provide an open auditing and monitoring system that lets any domain owner or CA determine whether certificates have been mistakenly or maliciously issued.
3) PreCertificates can’t protect users (as much as possible) from being duped by certificates that were mistakenly or maliciously issued.
4) PreCertificates can’t be installed on servers as they are not trusted.
5) PreCertificates doesn’t consist of an SCT parameter which is present in SSL certificates.
6) Mis-issuance of PreCertificates is treated on par with mis-issuance of the final certificates.
7) A PreCertificate is defined with a “poison extension” to the X.509 format. It is named this because it is an extension marked as critical (meaning that if it can’t be correctly parsed the certificate is to be treated as invalid) and was designed to not be supported by client software.
8) When browsers or operating systems encounter this extension they are not understood by them and hence they will be treated as invalid.
9) A PreCertificate, which contains the same data but is formatted a specific way so that it is not treated as a valid SSL certificate.
10) An attacker can steal the relevant data from PreCertificate as its a duplication of real SSL certificate.
The End of 1-Year SSL Certificate Validity: What Organizations Need to Know