
A self signed SSL certificate is an SSL Certificate which is been issued by an individual, who identifies its own identity. In other words, a self-signed certificate is the one that is created in-house using a tool like OpenSSL, self-signed certificate generator, etc instead of requesting it from a trusted public certificate authority (CA).
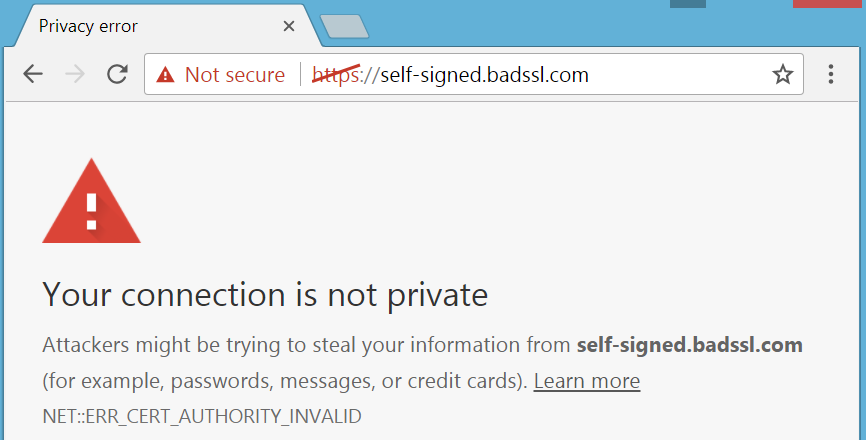
Technically, a self-signed certificate is not signed by any known or Private CA and there is not a certificate chain in it. Self-signed SSL isn’t trusted by any applications/operating systems. The browsers showcase an error while using a self-signed certificate.
Apart from the browser showcasing an error, there are many more risks involved in using a self-signed certificate. By the end of this article, you will understand why you should not use a self-signed certificate and where the risk lies when used.
The main reason why people go for a self-signed certificate is that its “Free”. However, a self-signed certificate is different from the “free SSL Certificate” provided by Let’s Encrypt.
Also Read: Risk of using a Free SSL Certificate
Free isn’t generally free. In some cases, the less cost attracts however accompanies downsides. In this way, how about we comprehend the danger of utilizing a self-signed certificate.
Many various browsers don’t support self-signed certificates as they not been signed by a trusted certificate authority (CA) like DigiCert, Sectigo, etc. Customers accessing sites bound to self-signed certificates lead to brand disgracing because browsers uphold their security parameters marking such sites dangerous when accessed leading to a frail number of customers or no customers at all who would likely want to access such sites.
In case of any breach, MITM attack or data alteration during transit the owner won’t be getting any warranty amount. However, SSL certificates issued by trusted CAs are backed by a certain warranty amount which instills confidence in the customers that they are in safe hands and their data security is of top priority.
A self-signed certificate is issued in-house and not by certified CAs hence the support isn’t available. The user must install by themselves and in-case of any error or threat, they must search for technical support which may cost them a lot.
The security alerts related to self-signed SSL Certificates drive potential customers for dread that the site doesn’t secure their identities. Both brand notoriety and client trust are harmed. This at-large effects the company’s security and makes it vulnerable to malware and other brand tarnishing threats.
Compromised Private Key poses a big threat to the organization. CA’s can go ahead and revoke the certificates issued by them. But in case of Self-signed certificates, organizations cannot revoke them. Instead, they replace it with another self-signed certificate. This inability to rapidly revoke the private keys can open the doors to major threats.
Self-signed certificates on intranet (e.g., employee attendance) also pose a threat as browsers do mark them insecure. Numerous organizations encourage workers to just disregard the alerts since they realize the inside site is sheltered, yet this can energize hazardous public browsing behavior. Employees acquainted with overlooking alerts on internal sites might be slanted to disregard warnings on public sites also, leaving them, and your association, defenseless against malware and different cyber threats.
If the private key of a self-signed certificate is comprised they are no ways you can revoke the certificate because it’s not vetted by a global CA. This will prompt critical outcomes both when utilized on public or internal sites.

The X.509 certificate chain for the self-signed certificate isn’t marked by a perceived certificate authority. On the off chance that the remote host is a public production site, this invalidates the utilization of SSL as anybody could set up a man-in-the-middle attack against the remote host. In the event that you are depending on a self-signed certificate, you may wish to consider getting an SSL endorsement from a confided in certificate authority like DigiCert, Sectigo.
Trusted certificates from CA’s is much secure than self-signed. They do offer a warranty, dedicated support, proper validation and browsers do support, unlike self-signed certificates.
Self signed SSL certificate – “Trust me – I am who I say I am”
Commercial SSL Certificate – “Trust me – Trusted Certificate Authority says – I am who I say I am”
From the above, understand which certificate you must use for your environment. I hope we have properly explained the risk involved in a self-signed certificate. Perhaps something is missing, do let us know.
The End of 1-Year SSL Certificate Validity: What Organizations Need to Know