The latest Phishing and Spoofing scam took away far more than just PayPal login credentials.
Understand the Phishing and Spoofing to secure yourself and your organization from such scams. Also, know how the latest PayPal phishing attack took place.
‘Phishing’ is an attempt by fraudsters to ‘fish’ for your personal/financial / investment details via email.
‘Phishing’ attempts usually appear in the form of an email appearing to be from a very known company to gain the reader’s trust. Within the email, you are then usually encouraged to click a link to a fraudulent page designed to capture your details.
While some e-mails are very easy to identify as fraudulent due to poorly designed and bad grammar, others may look legitimate sources. However, you should not rely on the name or address in the “From” field alone, as this can be easily manipulated. For example, look at the below image, which looks to arrive from PayPal asking you to take some action.
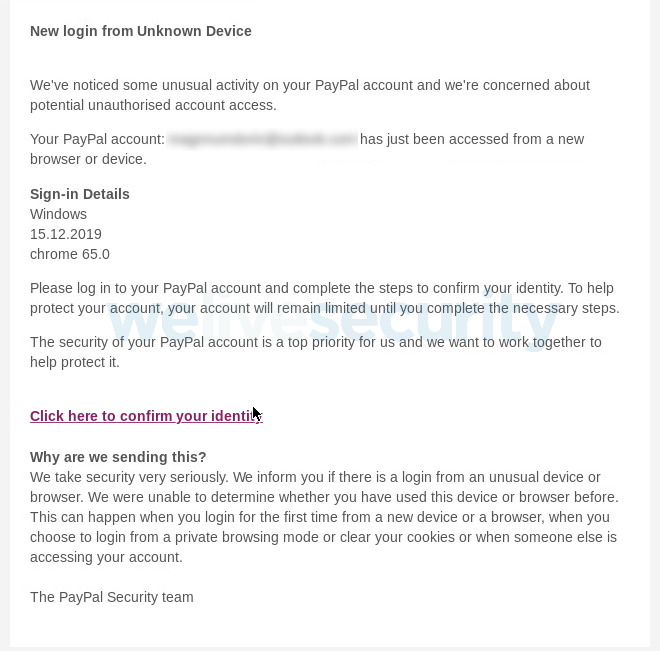
(image source: https://www.welivesecurity.com/wp-content/uploads/2019/12/Fig-1.png)
However, one must be very careful about the link destination i.e. if you hover on the link then it would be enough for you to identify the authenticity of this email.
Although it can be difficult to spot, ‘phishing’ emails generally ask you to click on a link which takes you back to a spoof web site that looks similar to the one mentioned in an email, wherein you are asked to provide, update or confirm sensitive personal information. To prompt you into action, such emails may signify a sense of urgency or threatening conditions.
The information most commonly sought through such means can be:
Recently, ESET researchers revealed an ongoing phishing scam that steeled all the important information by pretending to be PayPal.
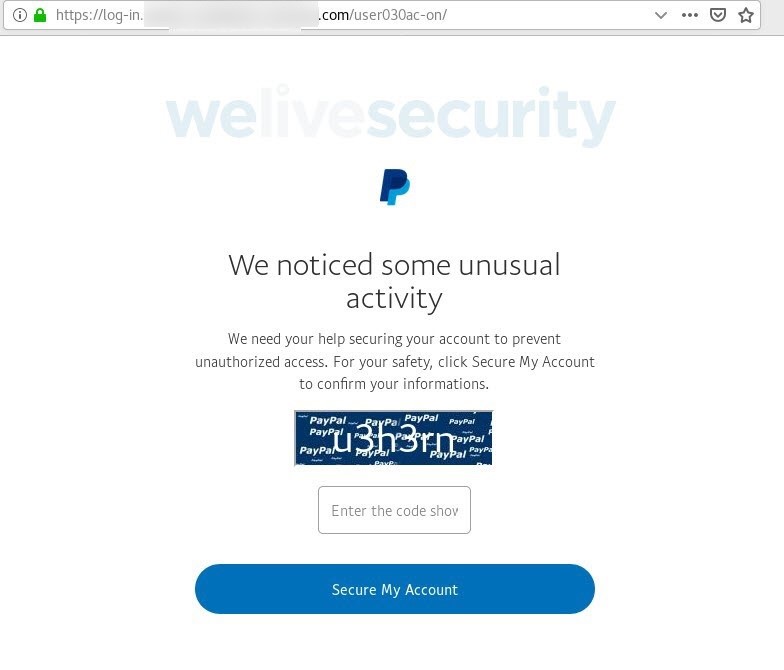
(image source: https://www.welivesecurity.com/wp-content/uploads/2019/12/Fig-2.jpg)
As mentioned above the attacker plotted the user by emailing an alert message “unusual activity” on your account, secure it by click on the link given.
On the click, it re-directed to a page that resembled the PayPal website. After that, it took away all the important details like PayPal login credentials, address, debit/credit card details, etc.
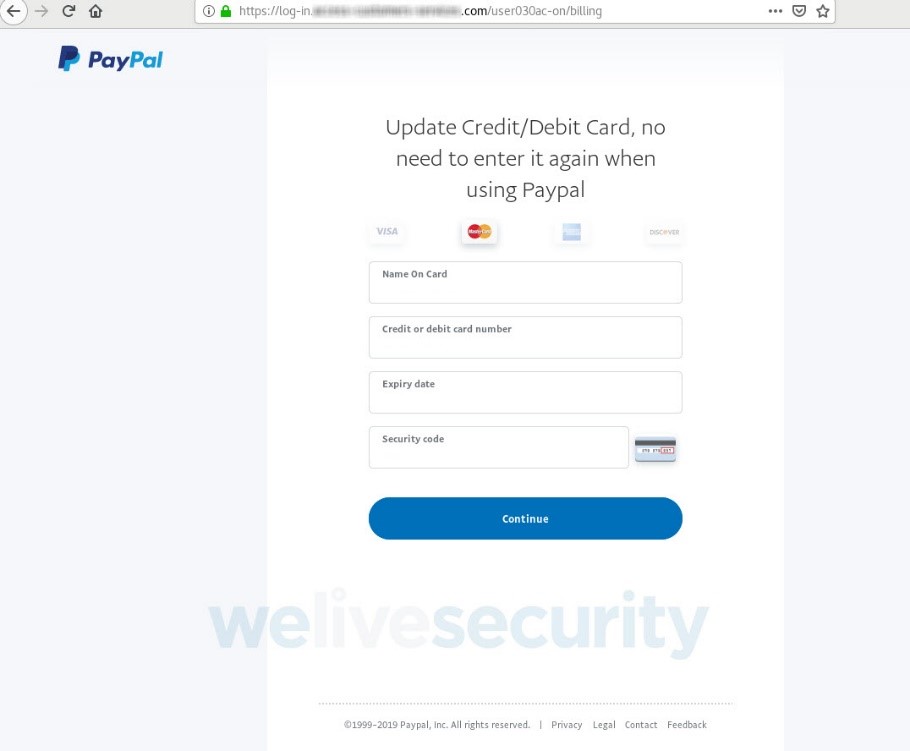
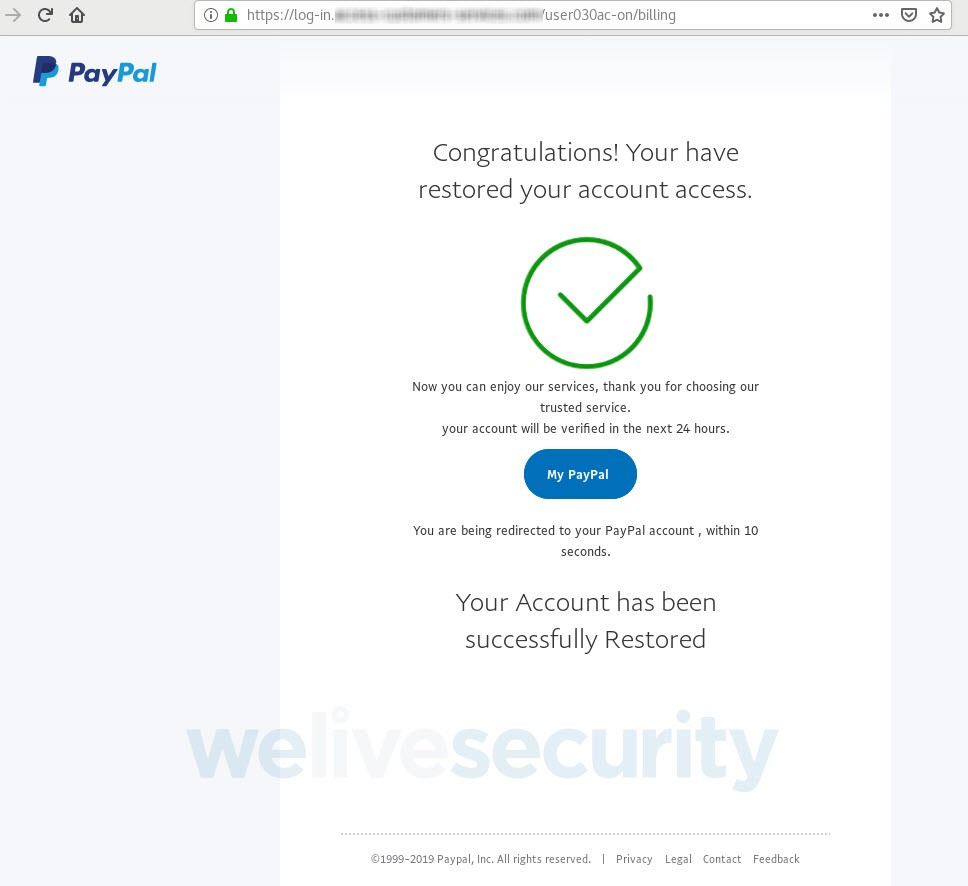
(image source: https://www.welivesecurity.com/wp-content/uploads/2019/12/Fig-7.jpg)
In the end, the attacker gives a message stating the account is been restored successfully. But the truth is your entire information is with the attacker.
(image source: https://www.welivesecurity.com/wp-content/uploads/2019/12/Fig-10.jpg)
Website spoofing is the act of creating a website, as a hoax, with the intention of performing fraud. To make spoof sites seem legitimate, phishers use the names, logos, graphics and even code of the actual website. They can even fake the URL that appears in the address field at the top of your browser window and the Padlock icon that appears at the bottom right corner.
Fraudsters send e-mails with a link to a spoofed fraudulent website asking you to update or confirm account-related information in the email only and submit. These emails also direct you to fraudulent Web sites and pop-up windows and try to collect your personal information.
This is done with the intention of obtaining sensitive account-related information like your User ID, Password, bank details, etc.
One way to detect a phony Web site is to consider how you arrived there. If you type, or cut and paste, the URL into a new Web browser window and it does not take you to a legitimate Web site, or you get an error message, it was probably just a cover for a fake Web site.
Below are the most important points to help to identify a genuine website:
There is a factor standard among web browsers to display a Padlock icon in the browser bar. This indicates the domain you are visiting is safe & secure, verified by the SSL Certificate Authority. In short, the website should be secured with an SSL Certificate.
![]()
After you have checked the padlock, check the type of SSL Certificate which is been used. Usually, the reputed website has an EV SSL Certificate on their website.
But if it is a phishing website it may use a Free SSL Certificate just to fool the user. Recently, Terence Eden a UK based technologist blogged a phishing scam that used a Free SSL certificate.
Also Read: Risk of a Free SSL Certificate
When browsing the web, the URLs (web page addresses) begin with the letters “http”. However, over a secure connection, the address displayed should begin with “https” – note the “s” at the end.
Must pay closer attention to the shortened links. The attacker often uses shorten links created from Bitly. Such shorten links are mainly used on social media for doing phishing activity.
Beware of the emails that tell you to do things urgently or gives any threats – from the attacker claiming to be a legitimate company.
Advised to read the email twice and look out for the punctuation, grammar errors. The phishing email is always with some grammar errors.
As a sometime reputed company do need something urgently. For example, eBay asked to change the password quickly after its Data breach in the year 2014.
As we know cybersecurity is increasing at a fast rate, but at the same time, the attacker is using intelligent tac-ticks to fool users (Except their English). They represent them to be a reputed company and still not only your login credentials but also card details, address and many more.
So, it’s very much difficult to identify such spam and save yourself from it. What’s the hack than to this problem? User needs to be aware of phishing and spoofing. All we need to do its exercise our skill of observation and be aware of the cybersecurity.
In case if you have come across any phishing emails or spoofing websites you can send the details at info@https.in we can help you protect your business against these crises.
Stand-up and report any phishing activity you notice. Time to fight together against such activity and secure our people from being spammed.
The End of 1-Year SSL Certificate Validity: What Organizations Need to Know