DPI (Deep Packet Inspection) is a technology which allows network owners to know the content of the Packet which is transmitted in real time. Which contains the origin and destination address along with other relevant info to move the packet across the network.
The introduction of DPI has drastically changed the process. Earlier the content sent by the user would reach the web server directly, with DPI in place the content, the content first goes to the Gateway device, decrypted and then scanned, subsequently encrypted and sent to the web server via the gateway device. Importantly duly scanned for content.
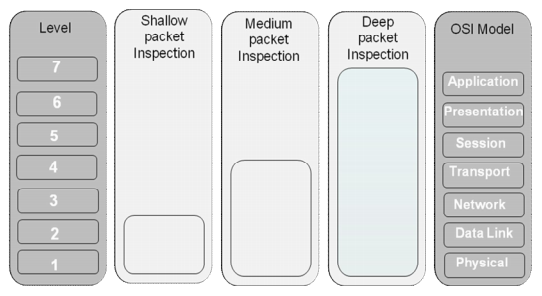
Functions provided by DPI technology available earlier to a limited extent depending on the level of packet analysis and are divided into three types which are ‘shallow’, ‘medium’, and ‘deep’ packet inspection.
SSL Certificate provides the benefit of using encryption to keep your private data safe from spying eyes. However, there are risks associated with its use since encrypted traffic can be used to pass through your normal defenses.
For example, you might download a file containing a virus during an e-commerce session or you could receive a phishing email containing a seemingly harmless downloader file which when launched, creates an encrypted session between client & server and downloads malware onto your computer. Because the sessions in these attacks are encrypted, they might get past your network’s security measures. Finally, the installation of the SSL certificate on the website becomes necessary for enabling the SSL Inspection which can prevent Hacking, phishing, malware attack etc. Here is an article which tells more about how PayPal website was used for the attack.
DPI brings intelligence in the network, which now allows surveillance of the content of the packet passing through the network. Enabling the I S Ps which use DPI to monitor, accelerate the speed or slow down, block or filter the information.
The End of 1-Year SSL Certificate Validity: What Organizations Need to Know