
SSL stripping is a technique by which a website is downgraded from https to http.
In other words, the attack is used to circumvent the security which is enforced by SSL certificates on https sites. This is also known as SSL downgrading.
The attacks expose the website to eavesdropping and data manipulation by forcing it to use insecure HTTP rather than secured https.
When you enter the URL on the browser, the first connection will be a plain http before it gets redirected to secure https. The attacker takes advantage of this small window by using the SSL strip attack.
Moxie Marlinspike, an ace computer security researcher, first demonstrated the attack and how can the https security be fooled. He was the Chief technical officer of Whisper Technologies which was later taken over by Twitter in 2011.
Http and Https are application protocols. Http transmits the data in plaintext whereas https sends data using a secure tunnel.
Now since you have got a fair idea about this SSL stripping, let’s understand how this actually works.
For SSL stripping to take place there are three requirements
Before I explain to you in detail here is the visual representation of it:
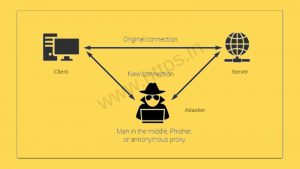
Victim V is made to believe that the data he is exchanging is secure and encrypted when transmitted over the network to the server. But the fact is there is no authenticity of data that is traveling because the encryption is stripped off and the data is in plaintext vulnerable to MITM.
(let’s example that with an example)
(Having understood how SSL stripping works I will guide you on the ways to prevent it.)
Also read: Recently Avast, the leader of IT security, revealed that around 700,000 routers around the world were diagnosed as vulnerable.
SSL certificates are a very secure way of transmitting data but as the technology grows with it comes the loopholes. These loopholes can indeed be addressed. Below are a few of the solutions
Also, Read Risks of not using SSL certificates for your webservers or any other internet-based applications.
(With this entire guide, we are trying to make this internet a safe place for you all)
The End of 1-Year SSL Certificate Validity: What Organizations Need to Know